The Rising Importance of Identity in IoT Security
As connected devices proliferate across industries, establishing a robust identity framework for each device has become fundamental to maintaining network integrity. Unique device identities enable precise authentication and authorization, ensuring only trusted nodes communicate and operate within the IoT ecosystem. This granular control helps mitigate impersonation and unauthorized access risks, which have been common attack vectors in recent cyber incidents involving IoT deployments.
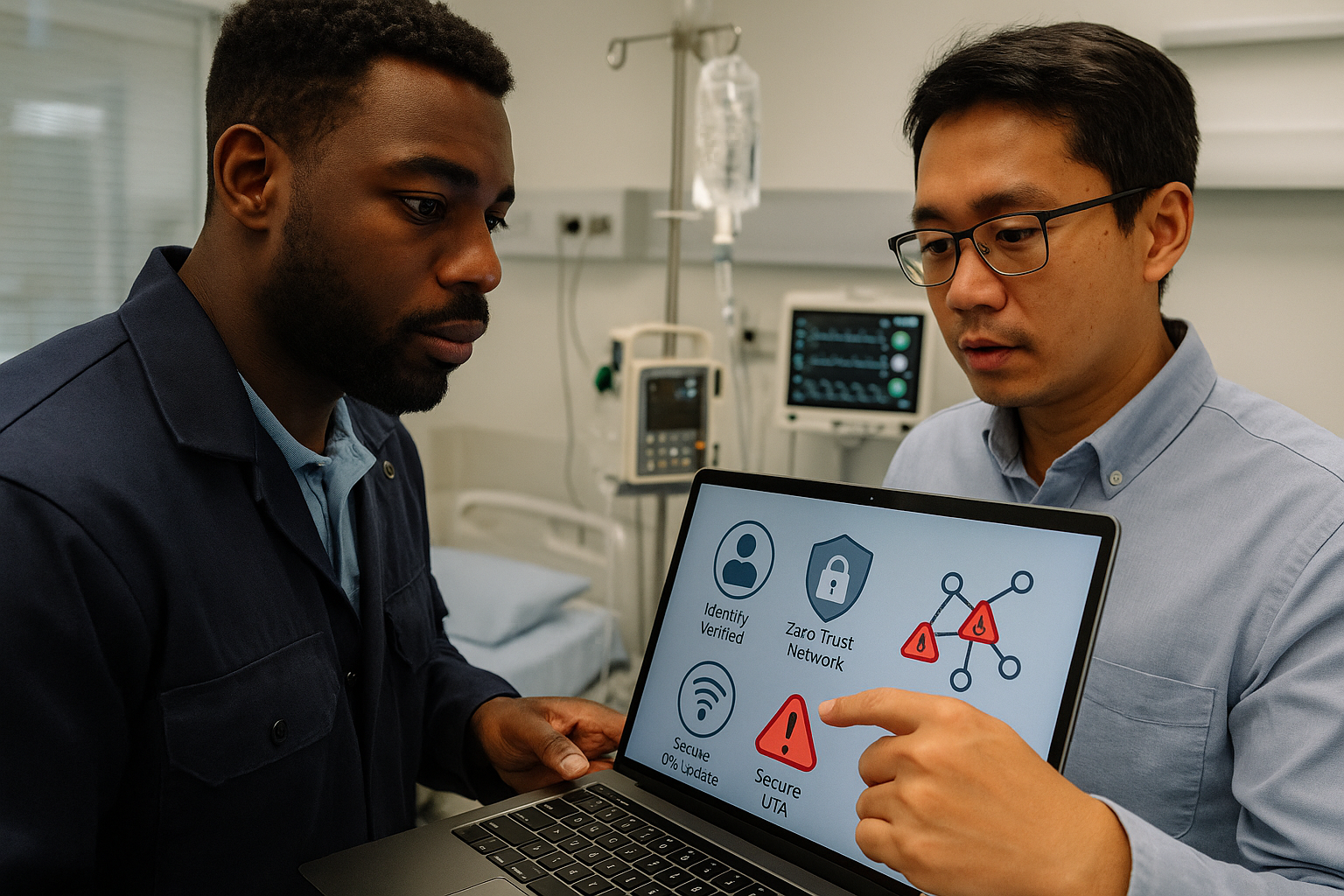
Zero Trust Architecture: A Paradigm Shift in Access Control
Traditional perimeter-based security approaches are increasingly inadequate given the expanding attack surface presented by IoT infrastructures. Zero Trust models, which operate on the principle of "never trust, always verify," require continuous authentication and strict access control regardless of device location or network segment. By implementing Zero Trust, organizations can compartmentalize their IoT environment, limiting lateral movement of threats and reducing the chance of widespread compromise.
Secure Over-the-Air (OTA) Updates and Continuous Monitoring
Timely and secure firmware updates are critical for patching vulnerabilities and improving device functionality. Secure OTA mechanisms ensure that updates are authenticated, integrity-checked, and encrypted during transmission, protecting against malicious code injection. Combined with real-time device telemetry and monitoring platforms, organizations gain comprehensive visibility into device health and performance. Health alerts triggered by abnormal metrics enable proactive maintenance and swift response, substantially minimizing downtime and optimizing field operations.
For instance, after widespread reports in 2026 detailed how insecure OTA updates led to operational disruptions across smart manufacturing environments, it became clear that integrating identity management, Zero Trust policies, and secure OTA protocols is no longer optional but a necessity.
For many organizations, events like this expose the same architectural weakness: data may exist, but it is not yet connected to a dependable operational process. Without that connection, teams see the issue too late or respond inconsistently across locations.
A practical engineering response should treat IoT Evolution World as a signal, not just a news item. The goal is to translate lessons from the event into clearer device telemetry, stronger automation rules, and dashboards that support decisions under real operating conditions.